-

Investment in Cybersecurity: A Crucial Component for International Business Success
Hitaarth
#AdvancedSecurity, #BusinessContinuity, #CompetitiveAdvantage, #CustomerTrust, #Cybersecurity, #CyberSecurityInsurance, #CyberSecurityInvestment, #CyberSecurityTrends, #CyberThreats, #DataEncryption, #DataProtection, #FinancialStability, #GlobalBusiness, #GlobalCollaboration, #IncidentResponse, #InternationalBusiness, #Investment, #RegulatoryCompliance, #RiskManagement, #SustainableBusiness, #TechInnovation, #ThreatIntelligence, #WorkforceTrainingOverview Investing in cybersecurity is vital for international businesses to protect their assets, maintain customer trust, and comply with global regulations. As businesses expand globally, they face diverse cybersecurity challenges that can impact their operations, reputation, and financial health. Key Areas of Investment in Cybersecurity for International Businesses 1. Regulatory Compliance 2. Threat Intelligence and
-
Understanding Common Cyber Threats and How to Protect Against Them
Hitaarth
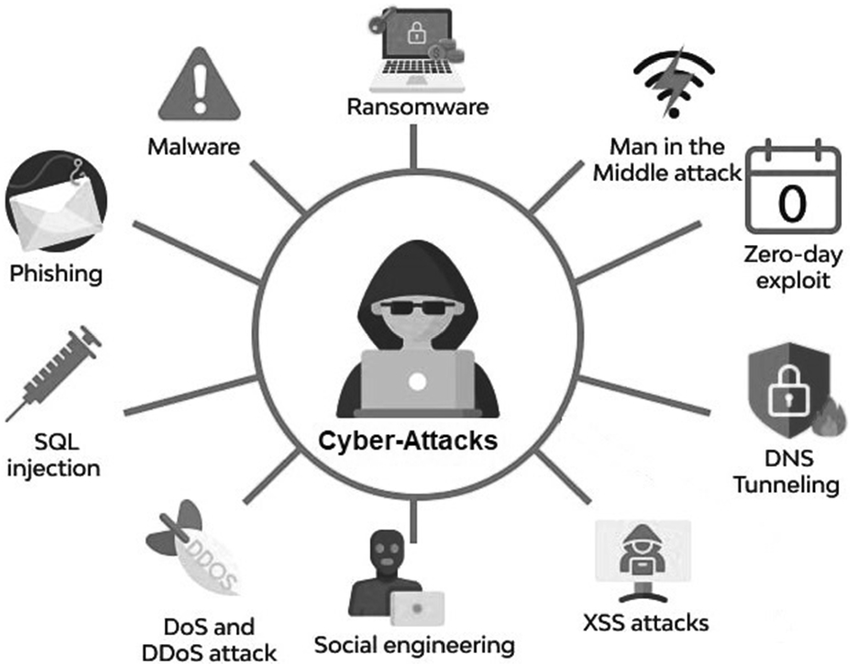
Introduction In the digital age, the landscape of cyber threats is continually evolving, posing significant risks to individuals and businesses alike. Understanding these common threats and knowing how to protect against them is crucial for maintaining security and safeguarding sensitive information. This blog will explore some of the most prevalent cyber threats today and provide
-
The Global Impact of Cybersecurity Breaches on International Business
Hitaarth
#BusinessSecurity, #CorporateSecurity, #CyberAttack, #CyberDefense, #CyberResilience, #CyberRiskManagement, #Cybersecurity, #CyberThreats, #DataBreach, #DataProtection, #DigitalSecurity, #EnterpriseSecurity, #GlobalBusiness, #GlobalEconomy, #GlobalImpact, #InformationSecurity, #InternationalBusiness, #ITSecurity, #SecurityBreach, #TechSecurityIntroduction In today’s interconnected world, cybersecurity breaches can have far-reaching consequences, especially for international businesses. As global enterprises expand and integrate their operations across borders, they become prime targets for cyber threats. Understanding the impact of these breaches and adopting robust security measures is crucial for safeguarding business interests. The Global Nature of Cyber Threats
-

A Shocking Wake-Up Call: Airtel’s Alleged Data Leak and the Importance of Cybersecurity
Hitaarth
#AirtelDataBreach, #AirtelLeak, #BreachResponse, #CustomerData, #CyberAttack, #CyberAwareness, #CyberResilience, #Cybersecurity, #CyberThreats, #DataBreach, #DataLeak, #DataPrivacy, #DataProtection, #DigitalSecurity, #HackAlert, #IncidentResponse, #InformationSecurity, #Infosec, #ITSecurity, #NetworkSecurity, #OnlineSafety, #PrivacyProtection, #SecureYourData, #SecurityBreach, #TechSecurity, #ThreatManagement, #VAPTThe recent news about Airtel’s alleged data leak, potentially exposing over 370 million customer records, has stirred significant concern. Although Airtel denies the breach, the incident underscores the critical importance of robust cybersecurity measures. This situation serves as a wake-up call for both organizations and individuals about the pervasive and evolving nature of cyber threats.
-

Steps to Take Immediately After a Cybersecurity Breach
Hitaarth
1. Identify and Contain the Breach Upon detecting a cybersecurity breach, the first crucial step is to identify and contain it. Use your security tools to pinpoint the breach’s entry point and determine its scope. Quickly isolate the affected systems to prevent further damage. This may involve disconnecting them from the network but avoid shutting
-

How to Secure Your Cloud Infrastructure
Hitaarth
Introduction In today’s digital age, cloud computing has become the backbone of many businesses, offering flexibility, scalability, and cost savings. However, with these benefits come significant security challenges. As more companies move their critical data and applications to the cloud, ensuring robust cloud security becomes paramount. Securing your cloud infrastructure is not just about protecting
-

How to Secure Your Business Against Cyber Threats
Hitaarth
Introduction In today’s fast-paced digital landscape, cybersecurity has evolved into a critical business priority. Cyber threats such as malware, phishing, ransomware, and insider threats have become increasingly sophisticated, posing significant risks to companies of all sizes. With the constant evolution of technology, it’s imperative to stay ahead of these threats to protect your business and
-

How to Secure Your Business Against Cyber Threats
Hitaarth
Introduction In today’s digital world, cybersecurity isn’t just an IT issue—it’s a business priority. Every day, cyber threats like malware, phishing, and ransomware become more sophisticated, posing significant risks to companies of all sizes. Understanding these threats and knowing how to combat them is crucial to keeping your business safe. Understanding Cyber Threats Cyber threats
-
The Critical Need for Cybersecurity Investments in Global Business
Hitaarth
#BusinessResilience, #BusinessSecurity, #CyberDefense, #CyberInfrastructure, #CyberInvestments, #CyberInvestmentStrategy, #CyberRisk, #Cybersecurity, #DataProtection, #DigitalSafety, #EnterpriseSecurity, #GlobalBusiness, #GlobalCyberDefense, #InvestmentInSecurity, #ITSecurity, #RiskManagement, #SecurityFunding, #SecurityInnovation, #TechSecurityIn today’s interconnected world, the importance of cybersecurity is paramount. As businesses expand globally, they must navigate an increasingly complex and vulnerable digital landscape. Cybersecurity is not just a technical requirement but a fundamental investment that protects a company’s assets, reputation, and operational continuity. Here’s why prioritizing cybersecurity investments is crucial for global businesses. Safeguarding
-
How to Create an Effective Incident Response Plan
Hitaarth
In today’s world, where cyber threats are constantly evolving, having a solid incident response plan (IRP) is essential for any organization. But what exactly is an incident response plan? Simply put, an IRP is a set of instructions and procedures that guide your team on how to detect, respond to, and recover from cyber incidents,
About

Lorem ipsum dolor sit amet, consec tetur adipiscing elit. Maecenas odio lacus, dignissim sollicitudin finibus commodo, rhoncus et ante.
Categories
Recent Post
- Toyota Admits 240GB Data Breach: A Wake-Up Call for Cybersecurity in the Automotive Industry
- Hackers Launch Cyberattack Against Ukraine’s Monobank: A Wake-Up Call for Digital Banking Security
- Elon Musk Claims X Faced DDoS Attack
- Deepfakes in 2024: Understanding the Threats and Mitigation Strategies
- Hacktivism in 2024: Emerging Trends and Challenges





